introduction: in recent years, "pig-killing plate" type of telecommunications fraud has continued to evolve, and some cases use overseas servers as back-end support. this article uses "pig-killing plate with servers in south korea" as the entry point, systematically explains the key points of identification and prevention, and helps the public and enterprises to be more vigilant.
"the server is in south korea" does not refer to a specific country, but refers to the fraud gang using servers located in south korea or labeled as south korea to host the fraud system. scams often use foreign hosts, cloud services and virtual machines to avoid supervision and improve anonymity.
the process usually involves establishing a false romantic or investment relationship, inducing trust, providing a "profitable" interface, and requesting prepayment or transfer. characteristics include excessive pursuit, rapid rapport, refusal to meet, and constant creation of reasons for urgent transfers.
technical means such as ip geolocation, whois information, domain name registration time, ssl certificate issuing authority and validity period can be used to initially determine whether the suspicious site uses a foreign server or has camouflage characteristics.

pay attention to communication delays, abnormal voice and video quality, the other party avoiding real-time video or using composite/spliced images, and the chat content avoiding specific personal information, which may be signs of fraud.
scams often require cross-border transfers, the use of overseas virtual bank cards, third-party payment or currency conversion. if the other party insists on bypassing formal channels for payment, you should be more vigilant and verify the other party's identity and payment account information.
if you are asked to install unknown apks, remote desktops, vpns or auxiliary software, there is a high risk of remote control, stolen credentials and tampered transactions. never grant remote access or enter banking passwords to strangers.
using overseas servers is not necessarily illegal, but fraudsters use cross-border hosting to avoid accountability. if you encounter clues about a suspected korean server, you should notify the local public security and network regulatory agencies, and professional channels will coordinate the investigation.
establish two-step verification of accounts, regularly check transaction records, do not disclose id cards and bank information at will, and suspend operations when encountering abnormalities and verify the authenticity of the other party through official customer service or relatives and friends.
once you suspect that you have been defrauded, immediately save the chat evidence, transaction vouchers and other party's information, apply to the bank to freeze/recover the funds and call the police. at the same time, submit the relevant domain name and ip information to a professional anti-fraud platform to assist in the investigation.
summary and suggestions: regarding "analysis of common telecommunications fraud techniques on how to identify and prevent pig-killing servers in south korea", the public should combine technical verification and common sense judgment, strengthen account protection, not trust cross-border fund instructions, and call the police and seek help from professional institutions in case of trouble. regularly paying attention to anti-fraud tips issued by the public security and banks is the most effective way to reduce risks.
- Latest articles
- an investor’s perspective on malaysian cn2 market trends and key points for evaluating mainstream service providers
- A Comprehensive Analysis of the Risks and Optimization Strategies for Enterprises Moving to Alibaba Cloud Hong Kong CN2
- interpretation of key indicators of vietnam cloud server data analysis and operation optimization roadmap
- a complete guide to japan’s native ip node purchase channels and price/performance comparison
- low-latency optimization strategy for cloud servers in southeast asia and cambodia in the edge computing era
- comparison of the latest price trends and price/performance evaluation of japanese cloud servers
- common troubleshooting and processing procedures in malaysia cn2 network environment
- comparative study on compliance, backup and security of vietnamese cn2 service providers
- availability zone selection and latency monitoring essential checklist for cloud server operation and maintenance in the eastern united states
- troubleshooting: quick diagnosis and solutions to common connection problems with vietnam vps ladders
- Popular tags
-
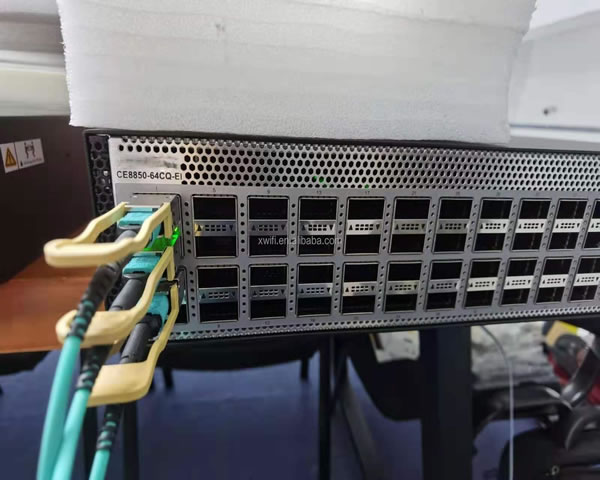
configuration and usage experience sharing of korean station group servers
this article shares the configuration and use experience of korean station group servers to help you better utilize the station group servers for seo optimization. -
Korean site group optimization website recommendation helps e-commerce business take off
This article discusses how Korean website optimization website recommendations can help e-commerce business take off and provide e-commerce companies with effective SEO strategies and practices. -
how effective korean kt servers can improve your online experience
this article explores how to improve your network experience with an effective korean kt server, covering aspects such as stability, speed, and security.